Onion Peel
Each layer hides a deeper truth, and your task is to peel them back one by one. The more layers you remove, the closer you’ll get to the flag hidden at the core.
We have 2 files
random_encodings.py:
import random
import base64
f=open("flag.txt","r")
flag=f.read()
for i in range(10):
choice=random.randint(1,2)
if choice == 1:
flag = base64.b64encode(flag.encode()).decode()
elif choice == 2:
flag = flag.encode().hex()
print(flag)
output.txt:
5458704e656b31365458704e656c56365458704e656b31365458704f616b31365458704e656b31365458704e656b31365458704e656b31365358704e656b31365458704e656b31365458704e656b31365458704e643031365458704e656b31365458706a656b31365458704e656b31365430524e656b31365458704e656b30775458704e656b35715458704e656c56365458704e656b31365458704f524531365458704e656b313654544e4e656b31365458704e656b31365558704e656b31365458704e656b35715458704e656b31365458704e4d4531365458704e656b31365458706a656b31365458704e656b3136546d704e656b31365458704e656b31355458704e656b31365458704e656b31365458704e656b31365458704e656b31365458704e656b313654544e4e656b31365458704e656b31365158704e656b31365458704e656b35715458704e656c6c365458704e655531365458704e656b313654587056656b31365458704e656b31365457704e656b31365458704e656b31365458704e656b31365458704e656b31365458704e656b31365458704f564531365458704e656b313654586c4e656b31365458704e656b31365933704e656b31365458704e656b31455458704e656b31365458704e4d5531365458704e656b313654587052656b31365458704e656b3136546c524e656b31365458704e656b30775458704e656b31365458704e656c46365458704e656b31365458704f616b31365458704e656b313654544a4e656b31365458704e656b31365258704e656b31365458704e656b35715458704e656b31365458704e656b31365458704e656b313654587052656b31365458704e656b3136546d704e656b31365458704e656b30795458704e656b35715458704e656b31365458704e656b31365458704f656b31365458704e656b313654586c4e656b31365458704e656b31365658704e656b30795458704e656b31555458704e656b31365458704e4d4531365458704e656b31365458705a656b31365458704e656b3136546d704e656b31365458704e656b30775458704e656b31365458704e656c6c365458704e656b31365458704e564531365458704e656b313654544a4e656b31365458704e656b31365358704e656b31365458704e656b35555458704e656b31365458704e4d6b31365458704e656b313654587052656b313654544a4e656b31365456524e656b31365458704e656b30775458704e656b35715458704e656b56365458704e656b31365458704f564531365458704e656b31365454464e656b31365458704e656b31365458704e656b31365458704e656b31715458704e656b31365458704e656b31365458704e656b313654587056656b31365458704e656b3136546d704e656b31365458704e656b31345458704e656b31365458704e656c6c365458704e656b31365458704e564531365458704e656b31365458704e656b31365458704e656b31365258704e656b31365458704e656b35555458704e656b31365458704e4e5531365458704e656b31365458706a656b31365458704e656b3136546e704e656b31365458704e656b30795458704e656b31365458704e656b31365458704e656b31365458704f524531365458704e656b31365454524e656b31365458704e656b31365933704e656b31365458704e656b31455458704e656b31365458704e4d5531365458704e656b31365458706e656b31365458704e656b3136546d704e656b31365458704e656b31355458704e656b31365458704e656c46365458704e656b31365458704f656b31365458704e656b313654544a4e656b31365458704e656b31365558704e656b31365458704e656b31365458704e656b31365458704e656b31365458704e656b313654587056656b31365458704e656b3136546c524e656b31365458704e656b31365458704e656b31365458704e656b31365458704e656b31365458704f616b31365458704e656b31365458704e656b31365458704e656b31365458704e656b31365458704e656b39555458704e656b31365458704e4d5531365458704e656b313654587042656b31365458704e656b3136546c524e656b31365458704e656b31345458704e656b31365458704e656b31365458704e4d6b31365458704f524531365458704e656b31365458704e656b3136546d704e656b31365554303d
If you read the python code, its pretty clear what its doing.
- Its choosing a random number(either 1 or 2)
- if its 1, it base64 encodes the flag
- if its 2, it encodes the flag in hex
- this runs in a loop 10 times
So its just an assortment of random hex and base64 encoding which can be reversed, the easy way would be to use cyberchef.
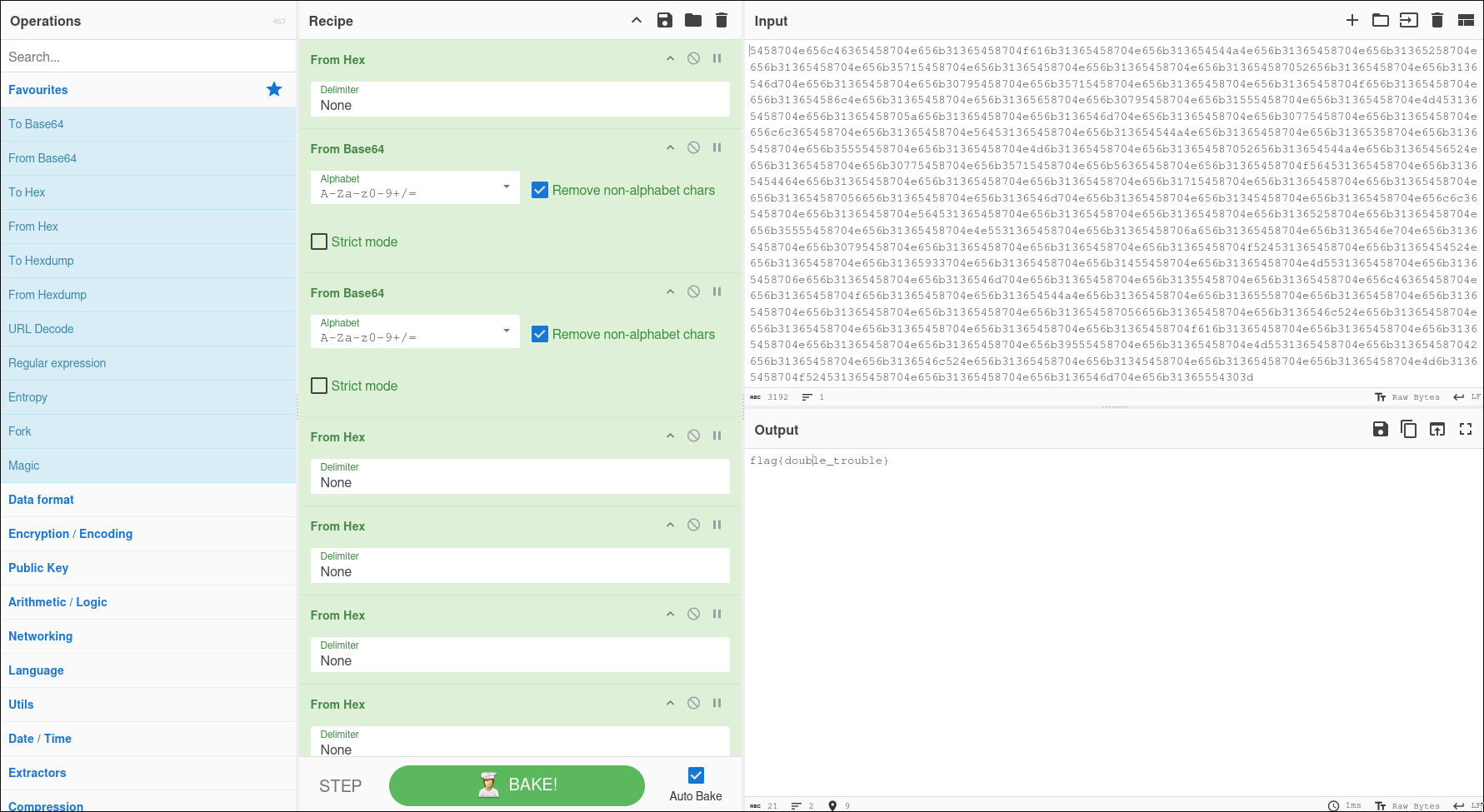
final flag:
flag{double_trouble}